倒序↓顺序↑
- 影片介绍
- 溢出OVERFLOW2未增删带翻译溢出OVERFLOW2未增(zēng )删(shān )带翻译(🤧)最(zuì )近,全(quán )球范(🐰)围内爆(bào )发(fā )了一场新的网(wǎng )络病毒攻击,被称为(wéi )溢出OVERFLOW2。这(zhè )种(zhǒng )病毒具有极高的危害性,严重威胁(xié )着全球网(🈵)络安全。溢(🗾)出(chū )OVERFLOW2是一种利用计算机程溢出OVERFLOW2未增删带翻(📒)译
溢出OVERFLOW2未增删带翻译
最近,全球范围内爆发了一场新的网络病毒攻击,被称为溢出OVERFLOW2。这种病毒具有极高的危害性,严重威胁着全球网络安全。
溢出OVERFLOW2是一种利(🗾)用计算机程序中的漏(💭)洞攻击系统的恶意软(🏝)件。通过对程序输入参数的不(😦)当处理,攻击者成功引(⛩)发缓冲区溢(🏡)出,从而控制计算机系统(🧀)。正如其名字所示,该病毒利用了程序(😉)中存在的缓冲区溢(🧠)出漏洞。缓冲区(📋)溢出是当程(🏽)序试图向一个长度有限的缓冲区写入过多数据时发生的一种情况,这可能会导致数据被写入到攻击者希望的内存区域,从而使攻击者能够执行恶意代码。
溢出OVERFLOW2的主(🏈)要攻击目标是操作系统和应用程序。它可以通过各种途径进入计算机系统,包括恶意邮件附件、不安全的网站下载和网络钓(🤗)鱼等。一旦感染,该病毒会在系统中植入恶意代(🎓)码(🐯),控制计算机并窃取用户的个(📍)人信息、银行账户等敏感数据。
溢出OVERFLOW2的危害性在于(🤙)其攻击手段的隐蔽性和(🥨)威力。攻击者可以通过该病毒获得对受感染计算机的完全控制,并通过远程控制使其成为“僵尸网络”的一部分。在“僵尸网络”中,攻击(⚽)者可以操纵大量僵(⏬)尸计算机发起各种网络攻击,如分布式拒绝服务攻(🔖)击(DDoS)和信息窃取。
要防范溢出OVERFLOW2的攻(🚵)击,最根本的措施是修补程序中的缓冲区溢出漏洞。软件开发者应(🥔)该在程序设计、编码和测试的过程中,严谨地遵循安全最佳实践,确保程序输入的正确处理和验证。此外,及时更新操作系统和应用程序的补丁也是防止病毒入侵的重要步骤。
对于普通用户来说,提高网络安全意识和避免点击可疑链接或下(💓)载未(🐫)知来源的文件非常重要。安装并定期更(🚸)新防病毒软件和防火墙也能提供额外(👧)的保护层。
溢出OVERFLOW2的(📅)威胁引发了全球网络安全专(👒)家的警觉。各国政府和互联网公司都加强了网络(🚰)监控和安全(🕝)防御,以确保用(⬆)户和企业的网络安全。此外,国际合作也是解决网络犯罪问题的关键,各国应加强信息(🌧)分享和合作,共同应对网络(🧣)安全挑战。
总之,溢出OVERFLOW2的威胁不容小觑,全球各界(📛)都应加强网络安全(🏍)意识和防御措施,以保护个人和企业的网络安全。只有通过合作努力,我们才能实(👴)现一个更加安全的网络环境。
Overflow2 Overflow Without Growth or Shrinking
Recently, a new global cyber attack has erupted, known as Overflow2. This virus poses a high level of threat to global cybersecurity.
Overflow2 is a malicious software that exploits vulnerabilities in computer programs to attack systems. By mishandling program input parameters, attackers successfully trigger buffer overflow, thereby gaining control over computer systems. As the name suggests, this virus exploits buffer overflow vulnerabilities in programs. Buffer overflow occurs when a program attempts to write too much data into a buffer with limited size, potentially allowing data to be written into a memory area desired by the attacker, enabling the execution of malicious code.
The main targets of Overflow2 are operating systems and applications. It can enter computer systems through various means, including malicious email attachments, insecure website downloads, and phishing attacks, among others. Once infected, the virus implants malicious code in the system, taking control of the computer and stealing the user's personal information, bank accounts, and other sensitive data.
Overflow2's harms lie in the stealthiness and power of its attack methods. Attackers can gain complete control over infected computers through this virus, turning them into part of a "botnet". In a botnet, attackers can manipulate a large number of zombie computers to launch various network attacks, such as distributed denial of service attacks (DDoS) and information theft.
The fundamental measure to prevent Overflow2 attacks is to patch the buffer overflow vulnerabilities in programs. Software developers should rigorously follow security best practices during program design, coding, and testing to ensure proper handling and validation of program inputs. In addition, timely updating of operating systems and applications with patches is an important step to prevent virus intrusion.
For ordinary users, raising awareness of network security and avoiding clicking on suspicious links or downloading files from unknown sources is crucial. Installing and regularly updating antivirus software and firewalls also provide an additional layer of protection.
The threat posed by Overflow2 has raised the alarm among global cybersecurity experts. Governments and internet companies worldwide have strengthened network monitoring and security defenses to ensure the cybersecurity of users and businesses. Furthermore, international cooperation is key to addressing cybercrime issues. Countries should enhance information sharing and collaboration to collectively tackle the challenges of network security.
In conclusion, the threat of Overflow2 cannot be underestimated. It is essential for all sectors worldwide to enhance network security awareness and defense measures to protect personal and corporate cybersecurity. Only through collaborative efforts can we achieve a safer online environment.
首先,我们(men )需要(yào )明(míng )确(què )的(de )是,心理学并(bìng )没有给予人们能够(🧕)直接读(dú )取他人(🥁)(rén )思想的能力。虽然我们可以(yǐ )通(tō(🕣)ng )过观(guān )察、推理(lǐ )和获(huò )取信息来对他人的思维(wéi )进行推测(cè ),但这并不意味(wèi )着(🥌)我们能够直接获取他(tā )们的(de )内心。心理学(🤭)家通过实验证(zhèng )明,我们(men )无法凭(píng )空(kōng )揣测他人(rén )的想法或(🦁)情(⬇)感,因为他们是(shì )个(gè )体独有(yǒu ),无法被(🤨)他人完全理(lǐ )解。
- 随便看看

笑功震武林下载
赵翊骁,林籽,吴旭东
剧情片
2024/中国大陆
HD

英语课代表的水真多视频免费1
保罗·路德,麦肯娜·格瑞丝,菲恩·伍法德,库梅尔·南贾尼,凯莉·库恩,比尔·默瑞,埃涅·赫德森,丹·艾克罗伊德,帕顿·奥斯瓦尔特,威廉·阿瑟东,塞莱斯特·奥康纳,洛根金,詹姆斯·艾克斯特,艾米莉·吴,艾米丽·阿琳·林德
喜剧片
2024/美国 / 加拿大
正片

十八格格_1
阿丽莎·威尔,梅丽莎·巴雷拉,丹·史蒂文斯,凯瑟琳·纽顿,凯文·杜兰,吉安卡罗·埃斯波西托,安格斯·克劳德,威廉·卡特列特,马修·古迪
恐怖片
2024/美国
抢先版

都市保安罗军免费阅读
吉冈睦雄,小日向星一,天野花,安井顺平,関幸治,川添野爱,石毛宏树,田畑智子,渡边一计
恐怖片
2024/日本
正片

六房直播
文雯 刘亭驿 董阿娇 纪姿羽
动作片
2024/中国大陆
正片
孪生公主第三部中文版全集
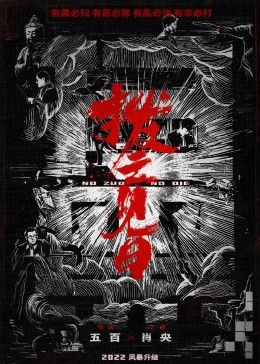
肖央 范丞丞
剧情片
2024/中国大陆
正片
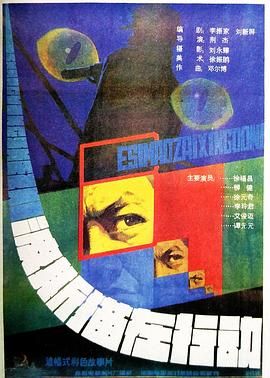
麻豆文化传媒网站77直播
李玲君,徐福昌,柳健,张秋歌
剧情片
1986/中国大陆
正片

再深点灬舒服灬太大了添视频软件
马昌钰,吴雄圻,谭伟民,许福印,陈志坚,冯明义,赵子岳,马崇乐
剧情片
1978/中国大陆
正片 上
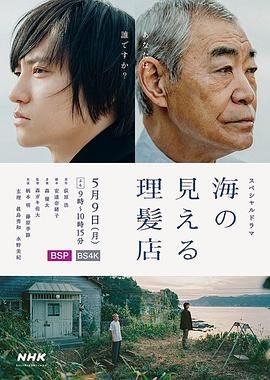
一夜残欢在线观看_1
柄本明,藤原季节,真岛秀和,水野美纪,玄理
剧情片
2022/日本
正片

之后电影高清在线观看_1
姚刚,栾元晖,刘帅良,孙爽,曾肖龙,田洺赫,王英麟,赵崇仁,张成龙,韩记伟,仇琳,栾佳琪
动作片
2025/中国大陆
HD

pendulum漫画
乔什·奥康纳,卡罗尔·杜阿尔特
喜剧片
2023/意大利 / 法国 / 瑞士
正片

顺博合金
妻夫木聪,渡边谦,原田知世,杉野遥亮,田中哲司,大政绚,满岛光
剧情片
2024/日本
正片